Forty-seven percent of AI-generated code contains security vulnerabilities, according to Palo Alto Unit 42 research. Vibe coding lets you ship fast — but shipping fast without a security audit is how you end up with a breach after launch.
Tekk's security review reads your actual codebase and finds the issues before your users do. Not a generic checklist. Specific file references, specific lines, specific fixes — grounded in how your app is actually built.
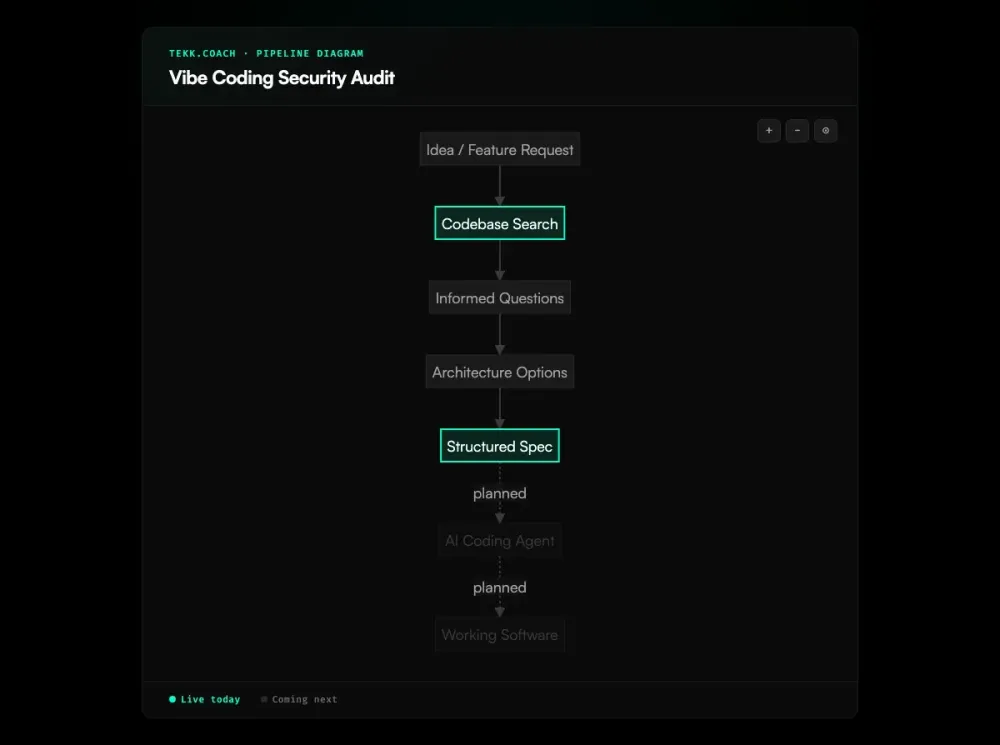
How Tekk Does a Vibe Coding Security Audit
When you ask Tekk for a security review, it doesn't run a pattern-matching scanner against your repo. It reads the code the way a security engineer would: looking at how authentication works in your app, how your database queries are constructed, where user input enters the system and whether it's validated before it gets anywhere sensitive. Teams that also want proactive quality control — not just reactive auditing — pair this with a vibe coding tool that generates structured specs before agents write a line.
Tekk searches the web for current CVEs and OWASP patterns specific to your stack. If you're on Next.js with Supabase and Stripe, the review is informed by what's actually risky in that combination right now — not what was risky in a generic Node app three years ago. Web research happens during the review, not before you started the project.
The output is actionable. Not "avoid SQL injection" — but "line 47 of auth.js constructs a query with unsanitized user input. Replace with a parameterized query." Every finding includes a file reference and a recommended fix. If there's nothing to fix in a category, it says so.
This is what Tekk's Expert Review mode is built for. You describe what you want reviewed, and the agent reads your codebase, applies security expertise, and produces a structured report you can act on immediately.
Key Benefits
Codebase-specific, not generic Tekk reads your actual files before generating a single finding. If your app doesn't have a payments flow, you won't get findings about Stripe misconfiguration. Every recommendation maps to something real in your repo.
Current CVE awareness Tekk searches the web during the review to surface vulnerabilities specific to your stack versions. A dependency you added last month may have a known exploit that wasn't in any model's training data.
File-level findings Every finding includes the specific file and line where the vulnerability lives. You hand the report to a developer and they know exactly where to go. No archaeology required.
Expert-level output without the consultant bill A security audit from an external firm costs thousands and takes weeks. Tekk produces the same depth of reasoning — grounded in your actual code — in the time it takes to have a meeting.
How It Works
Step 1: Connect your repo Link your GitHub, GitLab, or Bitbucket repository. Tekk supports all three. The connection is read-only for the review — Tekk never writes to your code.
Step 2: Ask for a security review Open a task in Tekk and describe what you want reviewed. "Do a security review of my auth flow." "Check the whole codebase for OWASP Top 10 vulnerabilities." "Focus on the API routes." You control the scope.
Step 3: Tekk reads the codebase The agent runs semantic search and file analysis across your repository — the same way it does for any planning session. It understands your stack, frameworks, and dependencies before generating a single finding.
Step 4: Web research on current CVEs Tekk searches for known vulnerabilities relevant to your specific stack and versions. This is what makes the review current — not frozen at training data from 18 months ago.
Step 5: Structured report with specific fixes Findings arrive as a living document in Tekk's editor. Each one includes the severity, the file and line reference, an explanation of why it's a vulnerability, and a concrete fix. You can edit the report, add notes, and hand it off directly.
Who This Is For
Vibe coders shipping to production You built something real with Cursor, Lovable, Bolt, or Replit. It works. Users are starting to sign up. You know you haven't thought hard about security — because the tool didn't make you. This is the moment to run the audit.
Non-technical founders who shipped with AI You used an AI coding tool to build your MVP and you're proud of it. But you don't have a security background, and you can't evaluate whether what the AI generated is actually safe. Tekk can. It tells you what's wrong in plain language and explains what to fix.
Anyone who shipped fast and needs a check You moved quickly. That was the right call. Now you're at the stage where "we haven't audited this" is a real liability — with investors, with customers, with compliance. A Tekk security review gives you a documented, actionable baseline.
What Is a Vibe Coding Security Audit?
Vibe coding is a style of software development where builders delegate most or all of the coding to AI tools — Cursor, Lovable, Bolt, Replit Agent, and similar — and iterate rapidly on the output rather than writing code by hand. The term was popularized in early 2025 and has since moved from novelty to mainstream: a significant share of new startups are built this way.
The productivity gain is real. The security gap is also real. AI models generate syntactically correct, functionally working code — but security is not their primary optimization target. They reproduce patterns from training data, and training data contains insecure code alongside secure code. The model doesn't know why a security check exists; if omitting it produces working code, it may omit it. Multiple 2025 studies put the vulnerability rate in AI-generated code between 45% and 62%.
A vibe coding security audit is a deliberate, structured review of an AI-generated codebase to find these vulnerabilities before they're exploited. The most common findings in vibe-coded projects map closely to the OWASP Top 10: injection vulnerabilities (SQL, XSS), broken authentication and session management, sensitive data exposure, security misconfiguration (missing headers, misconfigured databases), CSRF, and SSRF. Because these are well-understood vulnerability classes, a thorough audit can find them systematically — including via a structured ai code review that understands your specific architecture rather than matching against a fixed rule set. The issue is that most vibe coders don't have the security expertise to run that audit themselves.
What a proper audit covers: input validation; authentication and authorization logic; database query construction; API key and credential handling; security headers; CORS configuration; dependency risk from AI-suggested packages; infrastructure configuration. A generic automated scanner catches some of this. An audit that reads the code contextually — understanding your specific auth design, your specific data model, your specific stack — catches more.
Frequently Asked Questions
What is a vibe coding security audit?
A structured review of software built primarily with AI coding tools — Cursor, Lovable, Bolt, Replit, and similar — to find security vulnerabilities before users are exposed to risk. It covers the same categories as any code security audit (OWASP Top 10, authentication, injection, sensitive data handling), motivated by the fact that AI-generated code has measurably higher vulnerability rates than human-written code.
What vulnerabilities do vibe-coded projects typically have?
The most common findings are OWASP Top 10 patterns: SQL injection, XSS (AI models fail on XSS in 86% of tested samples), broken authentication (especially when AI places security logic on the client side), missing security headers, missing CSRF protection, and SSRF. Sensitive data exposure via misconfigured databases — Supabase, Firebase — is a well-documented real-world failure mode. A December 2025 systematic audit found all five of these in every tested app.
How does Tekk's AI security audit for code work?
Tekk reads your codebase first — semantic search, file analysis, repository profiling. It then searches the web for current CVEs relevant to your specific stack and versions. The output is a structured report with severity ratings, file and line references, and concrete fixes. Not generic advice; findings grounded in your actual app. Teams that want to reduce risk before it accumulates can complement the audit with spec driven development workflows that constrain what agents build in the first place.
Does Tekk check for OWASP Top 10 vulnerabilities?
Yes. Tekk applies OWASP Top 10 patterns to your specific codebase. Because it reads your actual code rather than running pattern-matching against known signatures, it can identify vulnerabilities that result from your specific design choices — not just the ones that match a static rule set.
How is Tekk's security audit different from automated scanners?
Automated SAST scanners (Snyk, Semgrep, Veracode) match patterns against known vulnerability signatures. Fast, but high false positive rates and no contextual reasoning. They can flag a SQL construction pattern but can't evaluate whether your auth design is fundamentally broken. Tekk reasons about the code the way a security engineer does — reading the design, understanding the flow, surfacing logic-level findings. The two approaches are complementary.
When should I do a vibe coding security audit?
Before you launch publicly. Before you handle real user data or payments. Before you raise a round — investors increasingly ask about security. The earlier you run it, the cheaper the fixes. If you've already launched without an audit, run it now; the findings tell you where to focus.
Ready to Audit Your Code?
Your vibe-coded project is further along than you think — and so is its security debt. Connect your repo, ask Tekk for a security review, and get specific, actionable findings grounded in your actual codebase.
No security expertise required on your end. That's the point.