You built fast with AI. The code works. Now you need to know if it's secure. Tekk.coach reads your actual codebase — not sampled files, not isolated functions, the whole thing — and runs a security review that finds what coding agents missed: missing input validation, broken auth patterns, hardcoded credentials, exposed endpoints, and more. You get specific findings with file locations, not a generic checklist.
[Try Tekk.coach Free →]
Key Benefits
Codebase-wide data flow analysis Tekk traces data from HTTP request handlers through validation layers, transformation logic, and database interactions. Vulnerabilities that span multiple files — the ones pattern-matching tools miss — are visible when you read the whole codebase.
Current best practices, not training data During a security review, Tekk searches the web for current best practices on your specific stack. Your Next.js auth implementation gets checked against current JWT security guidance, not patterns from two years ago. Your Node.js API gets reviewed against current OWASP guidelines.
Findings with file references and specific fixes
Every finding includes the file path, relevant code, and a specific recommendation. Not "consider validating inputs" but "validate and sanitize the email field at src/lib/auth.ts:23 before passing it to the magic link generator."
The senior security engineer you don't have A full-time security engineer costs $200k+. A professional security audit costs $5,000–$50,000 and gives you a point-in-time snapshot. Tekk gives you an expert review grounded in your actual codebase, on demand, for the specific areas you're worried about.
Especially valuable for AI-generated code Coding agents optimize for functionality — they write code that works. Security is a separate concern that requires threat modeling, not just implementation. Research shows AI-generated code introduces 1.7x more bugs than human-written code, including critical security issues. A security review catches what the coding agent didn't optimize for.
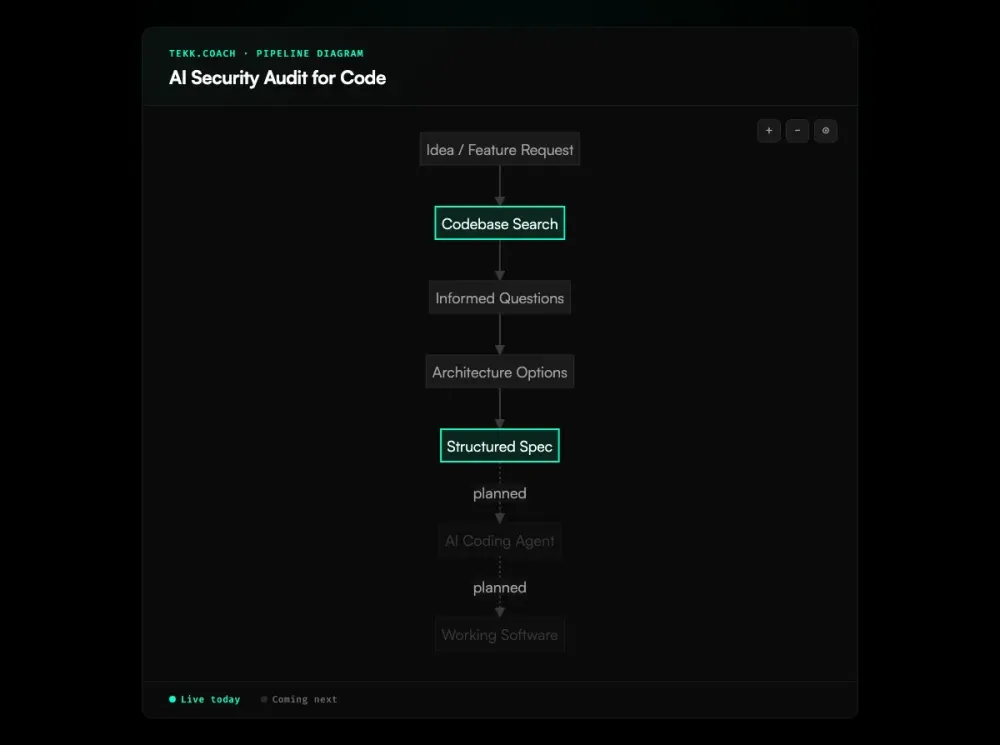
How It Works
Step 1: Connect your repository Connect GitHub, GitLab, or Bitbucket. Tekk runs a full repository profile — identifying languages, frameworks, services, packages, and architectural patterns — before touching any review.
Step 2: Request a security review In the Tekk interface, request a security review. You can scope it: "security review the authentication module" or "review the entire API layer for vulnerabilities" or "check our payment integration for security issues."
Step 3: Tekk reads the codebase Before generating a single finding, Tekk searches your codebase using semantic search, file search, and regex lookups. It builds a picture of how your application handles data — where it enters, how it's validated, how it's stored, how it's returned.
Step 4: Tekk searches current best practices Tekk searches the web for current security best practices relevant to your stack. Your specific framework, ORM, auth library, and deployment pattern inform the review — not generic guidance.
Step 5: Findings land in the living document editor The security review output is a structured document in the task editor. Findings include file references, code snippets, severity context, and specific fixes. You can edit, annotate, and share the document. It's the artifact you work from to address issues.
Step 6: Fix, re-review, iterate After addressing findings, request a follow-up review on the affected areas. Tekk reads the updated code and confirms fixes. The living document reflects what's been resolved.
Who This Is For
Vibe coders who shipped fast with AI You used a vibe coding tool to build quickly. The product works. But as Dark Reading reports, security pitfalls are multiplying as AI agent adoption accelerates — and you know "works" and "secure" are different requirements. A security review before you expose this to users — especially users with real data — is the responsible next step.
Solo founders pre-launch or pre-funding You're about to put this in front of real users, or in front of investors doing technical due diligence. You need to know what's in your codebase. You can't afford a $20,000 security audit. You need expert findings grounded in your specific code.
Small teams without a security engineer Security engineering is a specialization. Your 5-person team doesn't have one. You have a smart developer who reads security articles. That's not the same as a dedicated security review of your actual codebase. Tekk fills the gap.
Developers adding new attack surface You just integrated a payments API, an AI agent layer, a webhook system, or a third-party auth provider. New integrations bring new attack surface. A targeted security review of the new integration catches issues before they're in production.
What Is an AI Security Audit for Code?
An AI security audit for code uses artificial intelligence to analyze a software codebase for security vulnerabilities — going beyond pattern-matching to reason about code behavior, data flows, and architectural risk. Pairing this with a spec driven development workflow upstream reduces the likelihood of insecure patterns entering the codebase in the first place. Unlike traditional Static Application Security Testing (SAST) tools, which check code against rule libraries and known patterns, AI-powered review can understand context: how a function is actually called, where data actually flows, and whether the combination of individually-reasonable choices creates a security problem.
The category emerged as AI capabilities matured enough to reason about code semantically. Snyk's DeepCode AI describes the shift from "lengthy scans producing false positives" to "real-time semantic code analysis delivering actionable suggestions." The practical difference: a SAST tool reports "possible injection in users.ts"; an AI security review explains exactly how the injection occurs and provides the specific fix.
The urgency increased with the rise of AI-generated code. Coding agents like Cursor and Claude Code produce functional code at high speed — but they optimize for functionality, not security. Veracode's 2025 GenAI Code Security Report found that 45% of AI-generated code samples failed security tests across OWASP Top 10 vulnerability categories. Code that passes tests and works in development may be wide open to injection attacks, have hardcoded credentials, or skip input validation that an experienced security engineer would have added reflexively. AI security review is the check that catches what AI generation missed.
Frequently Asked Questions
What does an AI security audit for code find?
The most common findings in codebases built with AI coding agents: missing input validation on API endpoints, unsanitized database queries (SQL injection risk), hardcoded credentials or API keys in source code, broken authentication patterns (weak tokens, missing expiration, insecure session management), missing rate limiting and CORS policies, verbose error messages that leak stack traces and system info, and insecure cryptographic practices (using Math.random() for security tokens, outdated algorithms). Findings vary by codebase — Tekk reads your actual code, not a generic vulnerability list.
How is Tekk's AI security review different from SAST tools like Snyk or SonarQube?
SAST tools scan files against rule libraries — fast and automated, but pattern-based. They produce long reports with false positives and require security expertise to interpret — and Snyk's AI Code Security Report found that only 10% of developers scan most AI-generated code for vulnerabilities. They don't understand your architecture or how your code actually flows. Tekk reads the entire codebase before generating findings, traces data flows across files, searches current best practices for your specific stack, and produces specific, actionable findings grounded in your code. You don't need to know which findings matter — Tekk explains them in context.
Is AI-generated code less secure?
It's not inherently less secure, but it has specific risk patterns. Coding agents optimize for functionality — they write code that works. Security is a separate concern that requires threat modeling beyond the immediate implementation task. Common patterns: agents implement auth without fully modeling the threat surface, generate database queries without parameterization, skip input validation because the test cases don't include malicious inputs, and hard-code credentials in early drafts that don't always get cleaned up. A security review specifically addresses these patterns.
How do I audit my vibe-coded codebase for security issues?
Connect your repository to Tekk, request a security review, and scope it to the areas you're most concerned about — authentication, API endpoints, database interactions, payment handling. Tekk reads the codebase, traces data flows, and returns specific findings with file references. Start with the critical paths: anywhere user data is accepted, stored, or returned; anywhere authentication or authorization decisions are made; anywhere external APIs are called.
Does Tekk's security review replace a professional security audit?
For high-stakes, regulated, or compliance-driven environments — no. Professional security audits include manual penetration testing, threat modeling workshops, and human expertise that AI can't fully replace. Tekk's security review is the right choice for solo founders, small teams, and pre-launch products that need expert findings without enterprise audit costs. Think of it as a first-pass expert review that finds the real issues in your actual code — not a compliance certification.
What vulnerabilities does Tekk's security review cover?
Tekk's security review is driven by what it finds in your codebase, not a fixed checklist. It covers injection vulnerabilities (SQL, command, expression language), authentication and session management weaknesses, hardcoded or improperly stored credentials, missing input validation and sanitization, access control issues (missing auth checks, IDOR vulnerabilities), insecure cryptographic practices, error handling that leaks system information, and architectural patterns that create security risk. The review searches current best practices on your specific stack, so findings reflect the current threat landscape.
How does Tekk read my codebase for the security review?
Tekk reads your repository using semantic search (embeddings for intelligent code discovery), file search, regex search for precise lookups, and directory browsing for structural understanding. It supports GitHub, GitLab, and Bitbucket. Before generating any findings, Tekk profiles the repository: identifying languages, frameworks, services, and packages. This full-codebase understanding is what allows it to trace data flows across multiple files and identify vulnerabilities in the interactions between components.
Ready to Try Tekk.coach?
Your AI-generated code probably works. The question is whether it's secure. Tekk reads your codebase, finds what your coding agents missed, and gives you specific findings with file references and fixes — not a generic checklist. Connect your repo and request a security review today.
[Start Planning Free →]